Am planning a controller to process custom resource definitions which hold all data. By using this method a separate standalone database will not be needed, and the solution can scale as much as desired by increasing resources of the cluster itself. Thousands of games? Millions of games? And if there isn’t really a limit, what’s performance going to be like? These scaling answers must be investigated.
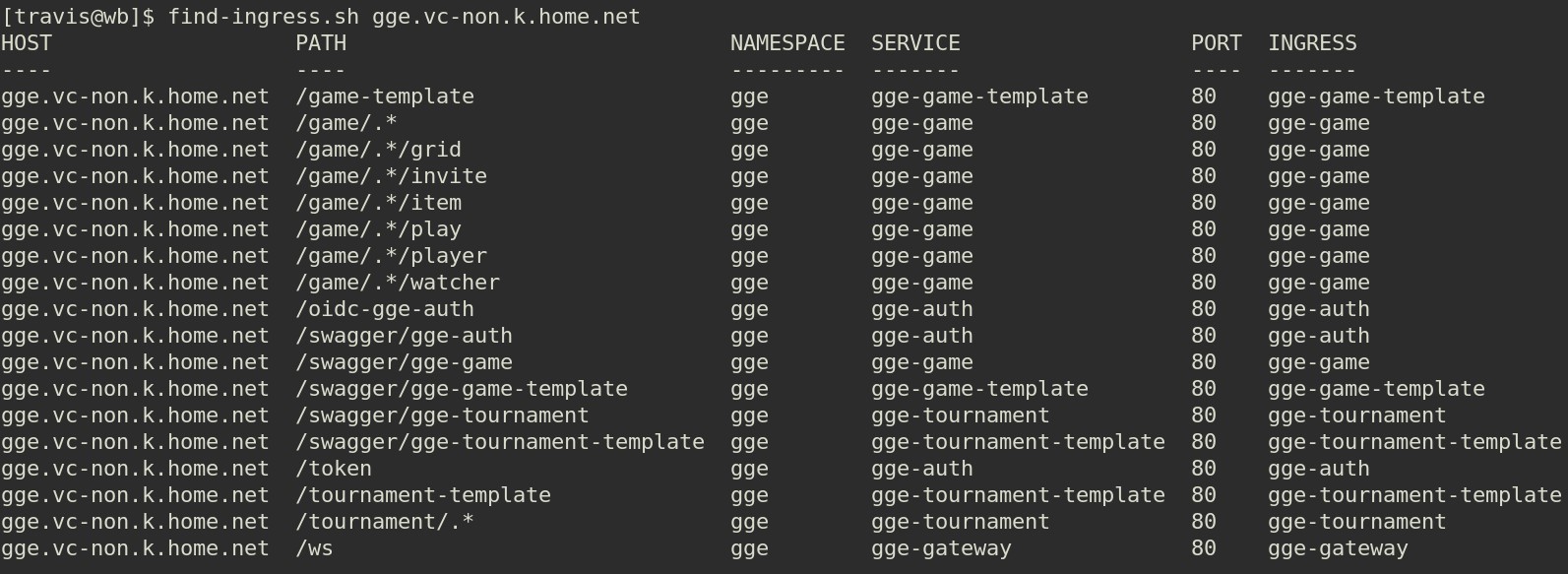
Besides the above, webapis, REST, OIDC, and ingresses mapped to appropriate paths will provide the infrastructure. Looking forward to experimenting more with scaling and high-availability methods provided by kubernetes.
Sure would be nice to work on open-source 100% of the time, wonder if there might be a way to make that happen …
Initial thoughts …
use cases:
- player 0 is always game controller (can do things with items)
- 2 players are 1,2
- 4 players are 1,2,3,4
- 2 player games
- 4 player games
- invite rejected
- invite accepted
- start game once enough players have joined
- send notice:
- game has started
- plays which have occured
- player finished their turn (if not real time strategy)
- if play was not allowed
maybe not:
- define a unit as unique?
crds:
---
boardgame.gge.aarr.xyz
invite.gge.aarr.xyz
event.gge.aarr.xyz ?
tic-tac-toe.game.gge.aarr.xyz
tic-tac-toe.play.gge.aarr.xyz (a controller for each game to process just that game)
reversi.game.gge.aarr.xyz
reversi.play.gge.aarr.xyz (a controller for each game to process just that game)
tournament.gge.aarr.xyz
- single-elimination.tournament.gge.aarr.xyz
- double-elimination.tournament.gge.aarr.xyz
[crd: boardgame.gge.aarr.xyz]
---
short: string
long: string
enabled: bool
path: string
[tic-tac-toe.boardgame.gge.aarr.xyz] (example instance)
---
short: "tic-tac-toe"
long: "Tic-Tac-Toe"
enabled: true
path: "/api/game/tic-tac-toe"
[crd: invite.gge.aarr.xyz]
---
game: string
user: string
[tic-tac-toe_<timestamp>.invite.gge.aarr.xyz] (example instance)
---
game: tic-tac-toe_<timestamp>
user: asdf <user being invited>
[crd: tic-tac-toe.game.gge.aarr.xyz]
---
owner: string
description: tic-tac-toe
is_invite_only: bool
is_public_view: bool
turn_type: string
allowed_num_players:
- <list>
invites:
- <list>{user: aaa, status: accepted}
- <list>{user: bbb, status: accepted}
grids:
- {id: 0, width: 3, height: 3}
players:
- <list>{id: 1, user: aaa}
- <list>{id: 2, user: bbb}
units: (available units in crd)
- id: 0
desc: string
ascii: string of length 1
imgsrc: <url>string
players:
- 1 (list of players allowed to use this unit)
actions:
- add (list of actions which may be performed)
attrs:
- (optional) list of name/value attributes
plays:
- <list>
[tic-tac-toe_<timestamp>.game.gge.aarr.xyz] (example instance)
---
owner: tloyd
is_invite_only: true
is_public_view: true
turn_type: round_robin
allowed_num_players:
- 2
invites:
- {user: aaa, status: accepted}
- {user: bbb, status: accepted}
players:
- {id: 1, user: aaa}
- {id: 2, user: bbb}
items: (units in play)
- {id: 0, unit: <id>, grid: 0, y: 1, x: 1, level: 0, player: 0}
- {id: 1, unit: <id>, grid: 0, y: 0, x: 0, level: 0, player: 1}
plays:
- id: 0
player: 1
plays:
- {id: 0, action: add, grid: 0, y: 1, x: 1, level: 0}
- id: 1
player: 2
plays:
- {id: 0, action: add, grid: 0, y: 0, x: 0, level: 0}
[tic-tac-toe.play.gge.aarr.xyz]
---
game: string
player: <id>
plays:
- <list>{id: 0, action: add, grid: 0, y: 1, x: 1, level: 0, unit: <id>}
[tic-tac-toe_<timestamp>.tic-tac-toe.play.gge.aarr.xyz] (example instance)
---
game: tic-tac-toe_<timestamp>
player: 1
plays:
- <list>{id: 0, action: add, grid: 0, y: 1, x: 1, level: 0, unit: <id>}